What Is A Method To Launch A Vlan Hopping Attack
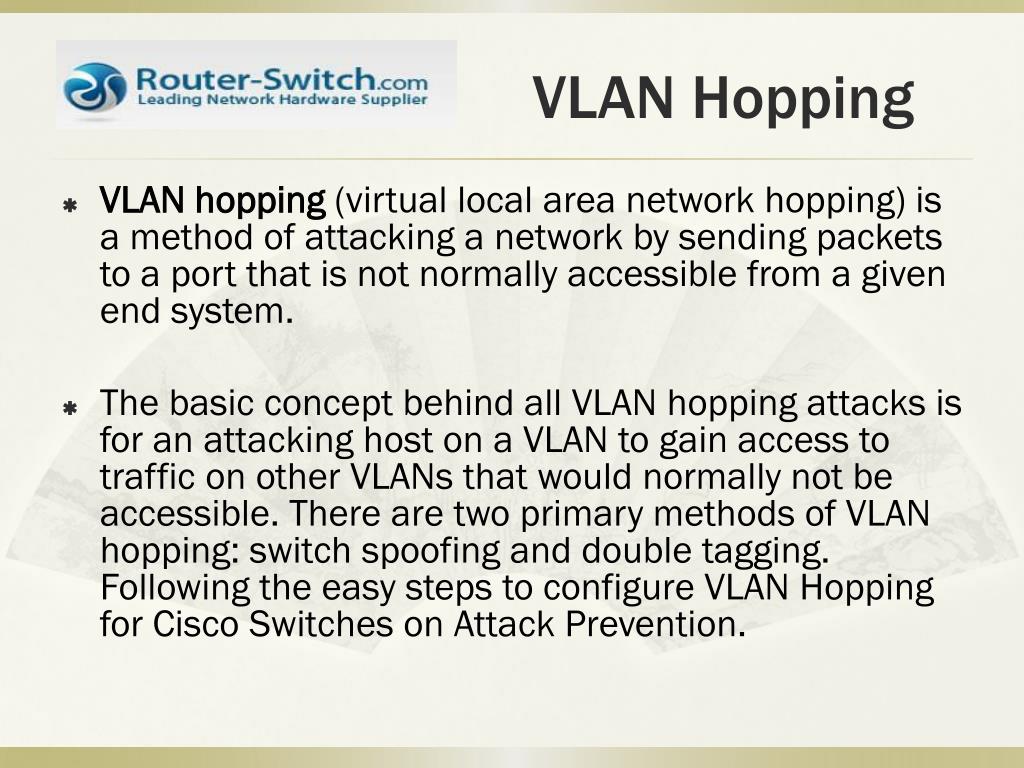
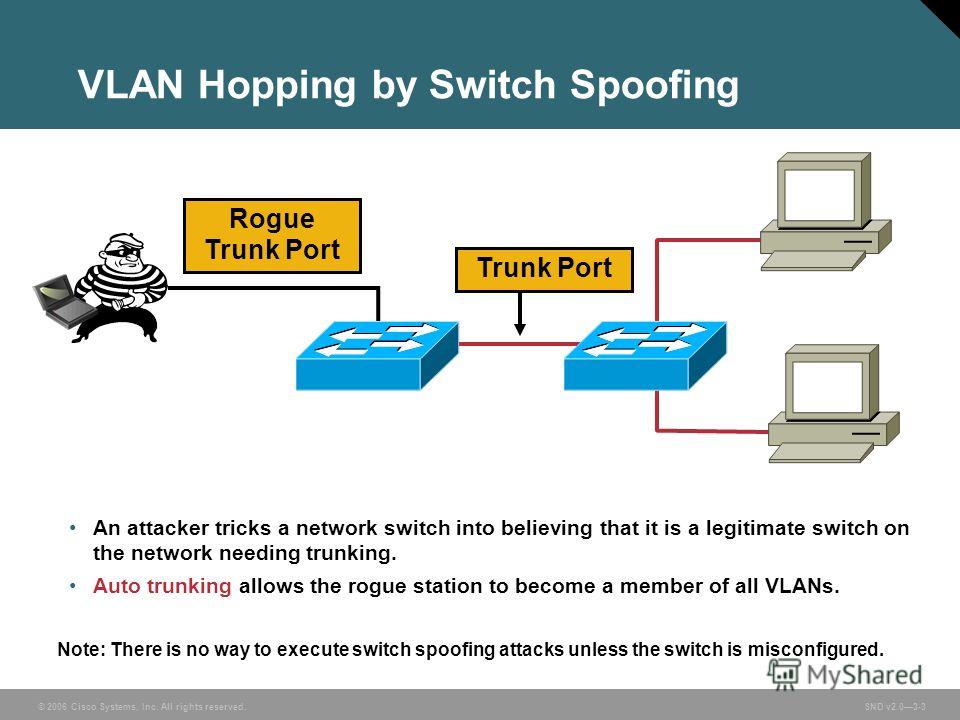
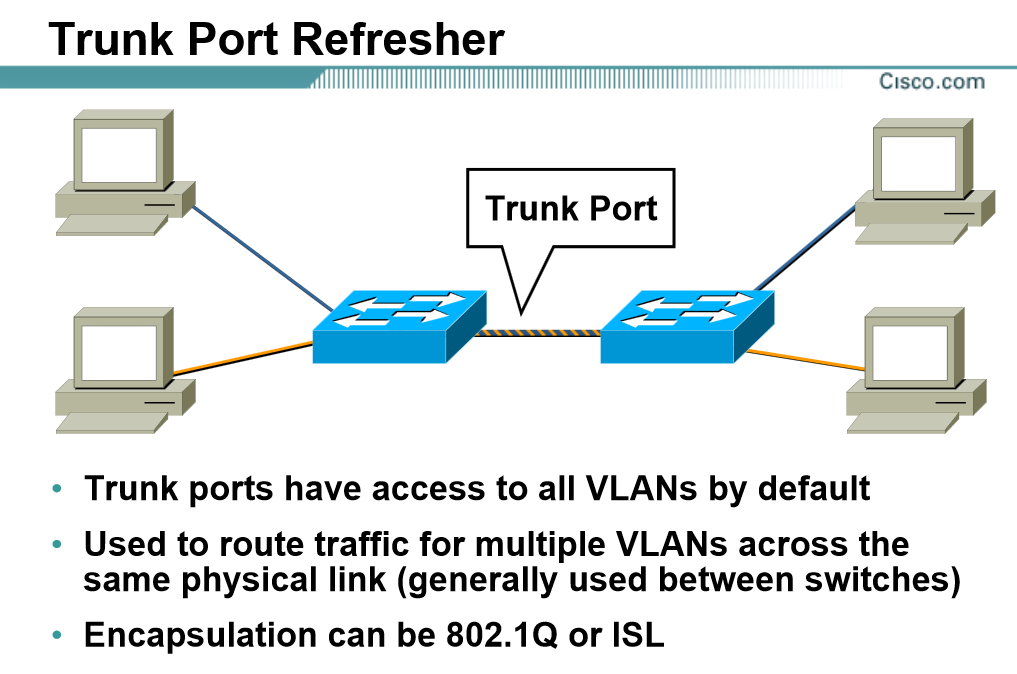
What Is A Method To Launch A Vlan Hopping Attack - Introducing a rogue switch and enabling trunking; What is a method to launch a vlan hopping attack? The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a.
The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. Introducing a rogue switch and enabling trunking; What is a method to launch a vlan hopping attack? A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a.
The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a. What is a method to launch a vlan hopping attack? Introducing a rogue switch and enabling trunking; A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of.
VLAN Hopping. Introduction by Ayushi Rathore Medium
A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a. What is a method to launch a vlan hopping attack? Introducing a rogue switch and enabling trunking; The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic.
PPT How to Configure VLAN Hopping for Cisco Switches on Attack P
Introducing a rogue switch and enabling trunking; What is a method to launch a vlan hopping attack? A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to.
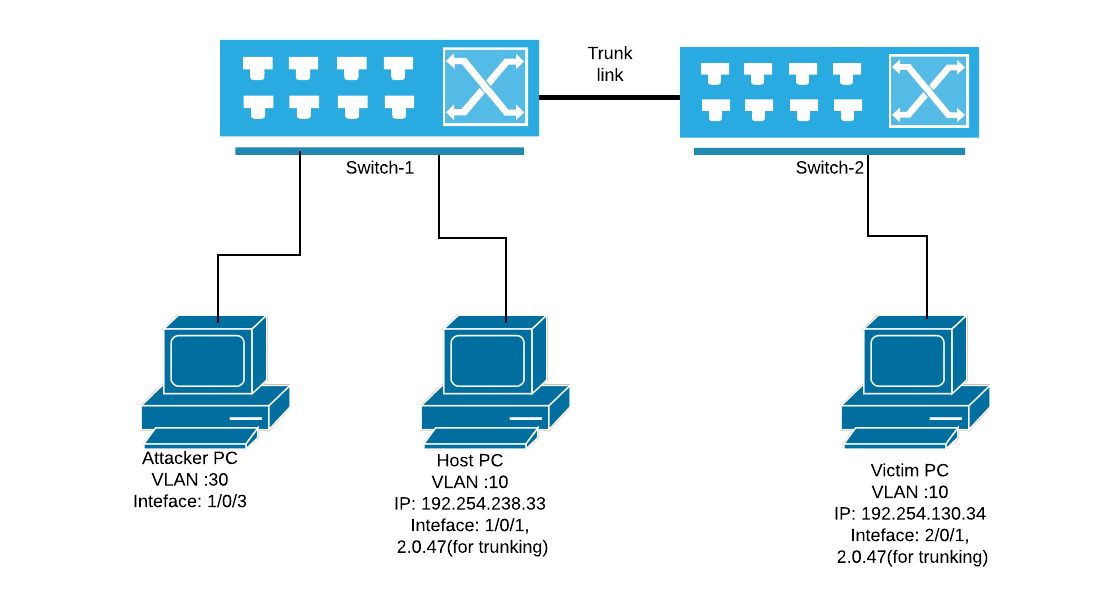
How to Configure Switch to Mitigate VLAN Attacks? Technig
The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a. Introducing a rogue switch and enabling trunking; A vlan hopping attack is where a device.
VLAN Hopping Attack NetMe
What is a method to launch a vlan hopping attack? A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. Introducing a rogue switch and enabling trunking; A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part.
VLAN HOPPING ATTACK
What is a method to launch a vlan hopping attack? The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. Introducing a rogue switch and enabling trunking; A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not.
VLAN Hopping Defeats Segmentation Oversitesentry
Introducing a rogue switch and enabling trunking; A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. A vlan hopping attack is a method.
LAN Attacks » CCNA 200301
What is a method to launch a vlan hopping attack? A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a. A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. Introducing a rogue switch and.
VLAN Hopping Attack Networking, Traffic, Network security
A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a. The fundamental idea behind all vlan hopping attacks is for an attacking host on one.
5. VLAN Hopping Attack & VLAN Types YouTube
The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a. What is a method to launch a vlan hopping attack? Introducing a rogue switch and.
A MustHave Guide RiskFree Protect Against VLAN and STP Attacks
The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. Introducing a rogue switch and enabling trunking; What is a method to launch a.
Introducing A Rogue Switch And Enabling Trunking;
A vlan hopping attack is where a device on one vlan can receive traffic from another vlan that it’s not a member of. The fundamental idea behind all vlan hopping attacks is for an attacking host on one vlan to get access to traffic on other. What is a method to launch a vlan hopping attack? A vlan hopping attack is a method used by cybercriminals to gain unauthorized access to network assets that are part of a.




.jpg?width=3840&name=1 (1).jpg)